VDI, DaaS, Virtual Workspaces: 4 reasons why BYOD may not be the way to go
As more and more companies embrace VDI and DaaS, there is always the question of what types of endpoints to provide them. The beauty of such solutions is that they deliver the user a simple, secure, and easily manageable virtual workspace to access company data and do their work. In the rush towards VDI and DaaS, vendors have introduced the notion that because the workspace is completely in the public or private cloud, users can use any device, and ultimately companies can adopt the concept of “Bring Your Own Device” (BYOD). This was further glamorized by VDI and DaaS vendor marketing teams, showing this in a very positive light, in a way that end users get the choice to bring any device and finance simply writes the check, really simplifying internal processes. After all, as long as you have a Citrix, VMware Horizon, or other VDI Client, users can gain access to their workspace, right? So, is BYOD the perfect choice for companies? Well, not always.
1. Security Concerns
When one thinks of endpoint security, the first thing that comes to mind is the attack surface. How could the device and its operating system be compromised? If users have the freedom to bring any device and decide on popular operating systems like Windows 10, Windows 11, or Mac OS, these systems can have vulnerabilities. Hackers have indeed mastered ways to penetrate read/write operating systems. If companies take responsibility for these endpoints, then there must be a serious investment in endpoint security solutions, to avoid malicious implementation of tools for spying for example, with potential risk for the virtual workspace. Also, if the company does not get involved at the endpoint, then any kind of poor user experience tied to weak security will affect IT. No doubt that users will blame the company provided cloud workspace over their own endpoint…
Users downloading infected programs on their local operating system is another serious threat for company data security. In a BYOD policy, the user feels legitimate to use its work device for personal matters, for example, to download movies or music, to work on personal applications…It is difficult for the company to control what happens locally on the device since the user by definition owns it and can do in theory whatever he wants on it.
It could be possible to prevent the user to make a screenshot or print the screen from the virtual session, with solutions such as Citrix. However, if the user has all the rights on the entire device, nothing can stop him from taking the screenshots he wants from the local session, even of the virtual desktop.
2. Operating System
In addition to security concerns, allowing users to choose any operating system brings forth another set of challenges. Operating Systems like Windows have so many moving parts and users who venture to mess with certain settings (i.e registry, installed applications, etc…) can interfere in the virtual workspace experience, thus affecting IT. If IT takes ownership of managing the PCs, they will need to make sure that proper GPOs are in place, and that apps are up to date. In that case, patch management tools may be required and this will add to IT expenses.
Even if IT have in theory no responsibility for the Operating system on the device in a BYOD policy, there is a plethora of situations that could end up affecting the user experience and cause a great deal of frustration for both the user and IT. Some examples include, when an upgrade of the OS version causing compatibility issues, local applications consuming too many resources, as well as problems connecting to the company peripherals such as printers or scanners.
3. Hardware Challenges
When users bring their own laptops or PCs, the hardware specifications can range, and this will have an ultimate effect on the experience. Virtual workspace clients for Citrix or VMware for example can be installed on most Operating Systems. However for the experience to be ideal, the device must offer enough resources (memory, CPU, etc..). A weaker machine will not be able to handle multiple applications, support multiple screens, or higher graphic and a higher screen refresh rate. Users may also need to connect PCs to various devices like printers, scanners, card readers, and more… As such, the endpoint has to be able to support this variety of peripherals.
With BYOD, having a heterogenous set of hardware can open up a lot of challenges if users bring very old machines that cannot perform.
4. Difficulty to manage endpoints centrally for IT teams
Even in a situation of VDI or cloud-based desktop infrastructure, it can be difficult for IT teams to manage centrally a very heterogenous set of devices. We saw in the previous paragraphs how the characteristics of the local session can affect the virtual workspace, both in terms of security and performance. Therefore, being able to see what happens on the device itself is an absolute necessity for the administrator, for troubleshooting, planning, or reporting purposes.
However, it is challenging to take control remotely, troubleshoot, perform updates, etc… on devices from a variety of brands, tech specs, or local configurations. VPN solutions may be useful, but are no panacea, and can represent an issue in terms of bandwidth or data privacy. To tackle these issues, companies would have to invest in centralized management tools for Windows such as Ivanti, with additional costs and complexity.
In conclusion, while BYOD is a great concept and allows greater flexibility for companies and their workforces, it can become a burden if it is not properly constrained. By restricting hardware criteria, IT departments can avoid a great deal of issues related to performance. Furthermore, IT departments can ensure that the endpoints are secure by making the right choice of local OS; one that is secure and read-only. Choosing the right OS will also further simplify day to day management of endpoints and make the necessary updates minimal. We can help you to achieve this with our solution ZeeTransformer, by ZeeTim
Why ZeeTransformer by ZeeTim is the right choice for your BYOD policy?
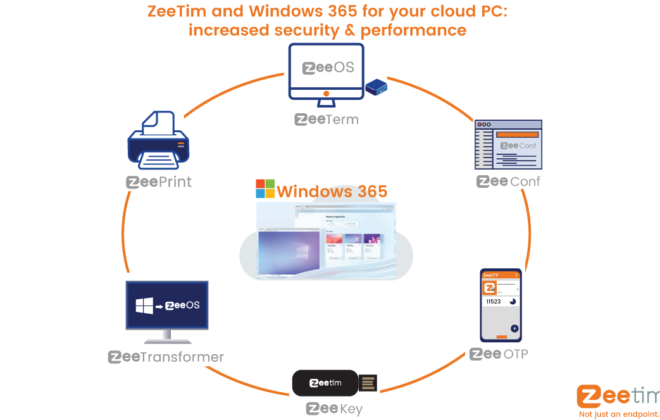
ZeeTim, a team of VDI experts has spent over a decade perfecting ZeeOS, an endpoint Operating System purpose build for VDI, DaaS, and Cloud Workspaces. This OS is ultra-secure and read-only making it nearly impossible for hackers to penetrate. It’s also an OS that provides users an optimized and simple experience to access their workspace and be productive. From an IT administration standpoint, management console ZeeConf was developed to ensure administrators could make all of the configurations necessary to any endpoint running ZeeOS, monitor, and remote support the endpoints from anywhere.
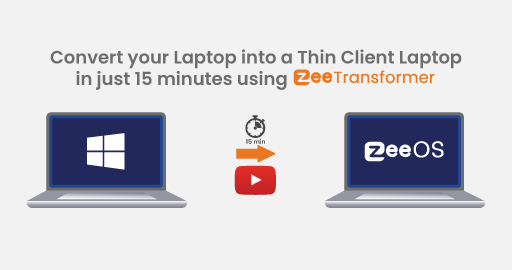
Thanks to ZeeTransformer, ZeeOS can be placed on any PC (x86 64bit) within 15 minutes. Try it for yourself using the ZeeTransformer tool!
How it works
With ZeeTransformer, your users can use a USB to boot securely on ZeeOS and then connect to their virtual workspace from it:
- No modification on local disk: temporary boot only. The user can go back to his usual desktop by simply removing the key
- Zero interaction between local OS and virtual workspace since the virtual workspace is run from a separate and secure OS
- ZeeOS is read-only: whatever the users do on their local OS, they cannot modify any configuration when they work on the USB key
- Minimal hardware requirements: apply to a large diversity of devices regardless of CPU or storage characteristics
- Possibility to manage all endpoints centrally thanks to management console ZeeConf (complimentary with any purchase of ZeeTransformer), with update management, troubleshoot, reporting info…

Search
Recent posts
- ZeeScan is now available on the VMware Marketplace 22 April 2024
- The main Cybersecurity risks of remote work: Safeguarding your infrastructure in a connected world 3 April 2024
- Introducing the latest version of ZeeScan! 22 February 2024
- Chromebooks in Business: Advantages and Challenges to Consider 19 February 2024
- Happy New Year from all of us at ZeeTim! 1 January 2024